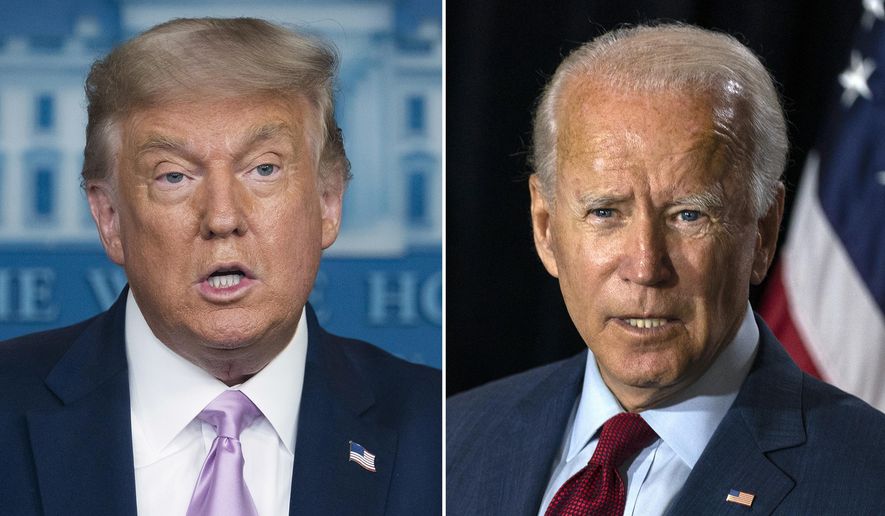
Cyberattackers from China, Russia and Iran have targeted the presidential campaigns of President Trump and Democratic rival Joseph R. Biden, Microsoft said Thursday.
The Iranian hacking group Phosphorus took aim at Mr. Trump’s campaign, and a Chinese group, Zirconium, targeted Mr. Biden’s campaign, according to Microsoft.
The Russian group Strontium — also known as Fancy Bear — the same military intelligence outfit that hacked the 2016 Democratic presidential campaign, has attacked more than 200 political campaigns, consultants, advocacy groups, and others, including the German Marshall Fund.
The attacks make “clear that foreign activity groups have stepped up their efforts targeting the 2020 election as had been anticipated, and is consistent with what the U.S. government and others have reported,” Tom Burt, Microsoft corporate vice president, wrote on the company’s website.
He said most of the attacks were stopped by the company’s security tools.
The Chinese group Zirconium attempted thousands of attacks from March to September, according to Microsoft, which yielded 150 compromised accounts. The Chinese cyberattackers, also known as Hurricane Panda, mainly focused on people “closely associated” with the presidential campaigns, including Mr. Biden’s and “at least one prominent individual formerly associated with the Trump administration,” Mr. Burt said.
Others targeted by the Chinese include several people in the international affairs and think tank sector, including at places such as the Atlantic Council and Stimson Center.
In May and June, Microsoft said the Iran-based attackers from Phosphorus tried but failed to log into accounts belonging to Mr. Trump’s campaign staff and Trump administration officials.
While Attorney General William Barr and National Security Adviser Robert O’Brien have said China represents the greatest threat to U.S. elections, cybersecurity professionals remain most concerned about the threat posed by Russia.
“The targeting of political organizations is a common feature of cyberespionage,” said John Hulquist, senior director of analysis at cybersecurity firm Mandiant Threat Intelligence. “Parties and campaigns are good sources of intelligence on future policy, and it’s likely Iranian and Chinese actors targeted U.S. campaigns to quietly collect intelligence, but [the Russian attackers’] unique history raises the prospect of follow-on information operations or other devastating activity.”
Microsoft’s election warning Thursday follows other alerts from the U.S. intelligence community. Last month, William R. Evanina, director of U.S. counterintelligence, warned that China, Iran and Russia had tried to influence public opinion about the November elections.
Mr. Evanina said China’s efforts involved pressuring political figures, while Iran and Russia spread disinformation.
The U.S. National Counterintelligence and Security Center found that China preferred Mr. Trump to lose and viewed him as unpredictable, and Russia wanted Mr. Trump to win, he said.
Sen. Ben Sasse, Nebraska Republican and a member of the Select Committee on Intelligence, said Microsoft’s alert shows that the U.S. needs to get tough.
“In Beijing, Chairman Xi [Jinping] wants Biden to win; in Moscow, [Russian President] Vladimir Putin wants Trump to win; both of these miserable SOBs have the same goal of turning Americans against each other,” Mr. Sasse said in a statement. “The United States needs to make it clear that China and Russia will face severe consequences for hacks and disinformation campaigns. Chinese communists and Russian oligarchs don’t get to vote in America’s elections.”
Acting Homeland Security Secretary Chad Wolf said Microsoft’s announcement affirms that the federal government’s approach to protecting the election and working with the private sector is paying dividends.
“DHS and this administration have been consistent in calling out all these bad actors and taking action wherever appropriate to protect the integrity of our election systems, reinforced by the Department of Treasury’s recent actions sanctioning four Russia-linked individuals for election interference,” Mr. Wolf said in a statement. “I applaud Microsoft’s efforts to defend democracy against these attacks and for their transparency on this critical issue.”
Microsoft said it took control of 25 internet domains in August that were used by the Iranian cyberattackers, after receiving permission from a federal court in the District of Columbia.
The company previously announced that it took control of domains last year that North Korean-linked cyberattackers used to target think tanks, government officials and others who work in the university and academic research sectors.
Last month, FBI special agent Matthew O’Brien told The Washington Times that the FBI had discovered foreign adversaries from Russia, China and Iran attempting to breach think tanks’ networks to spot and assess reliable sources of information and surveil the policy debates in Washington. The agents have preyed on Washington think tanks, including by “spoofing” websites associated with a think tank, which involves designing a fake website to look like the real one and then spreading bad information to unsuspecting visitors.
• This article is based in part on wire service reports.



Please read our comment policy before commenting.